Don’t look now but there’s another massive vulnerability on the loose and this time it’s your Mac that’s under fire. Shellshock, the newly-discovered vulnerability affects Mac and Linux machines by allowing an attacker to inject code directly into your machine.
This vulnerability is one of the worst found yet, as it has the chance to affect not only webservers and desktop machines, but even smaller web-connected devices like Wi-Fi cameras, security systems, and any other Internet-of-things devices running web-enabled bash scripts on them.
There is a fix, but before getting to that, here’s a little bit on what Shellshock actually is, then we’ll get you patched.
What is Shellshock?
So what exactly is this Shellshock vulnerability? Without getting too technical, Shellshock affects something called Bash. Bash is basically what Terminal on your Mac uses to run commands and is technically called a Unix Shell.
The issue with Shellshock is that an attacker could use the vulnerability to pull private data from your machine or inject malicious code into your machine, all in the background and all done remotely.
So why all the fuss now? Well, a team at Red Hat happened across the bug completely by mistake and now that it’s found, experts realized that basically any Mac or Linux-based system is vulnerable, and has been for more than 20 years.
Not only affecting desktop machines, devices as low on the chain as your router and cable modem are affected by the bug, too. Yea, like we said, it’s pretty big.
Check to See if You’re Vulnerable
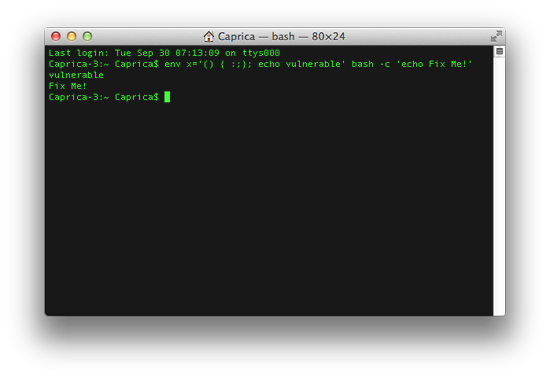
While it’s nearly impossible to check all your devices for the vulnerability, it’s actually pretty easy to check your Mac. All you have to do is open up Terminal and run this command:
env x='() { :;}; echo vulnerable' bash -c 'echo Fix Me!'
You’ll get one of two results from this command. If you’re patched and safe you’ll see:
bash: warning: x: ignoring function definition attempt bash: error importing function definition for `x' hello
But if like most machines you’re not patched and in danger, you’ll see this:
vulnerable Fix Me!
Now that you checked on your vulnerability, it’s time to get you fixed.
(Thanks to LifeHacker for the testing code)
What to do About It
If you’re reading this, there’s a pretty good chance you’re using a Mac, so we’ll cover how to update your Mac as the primary way of fixing the issue. IF you have any Linux machines that need updating however, check here for instructions on getting your machine patched.
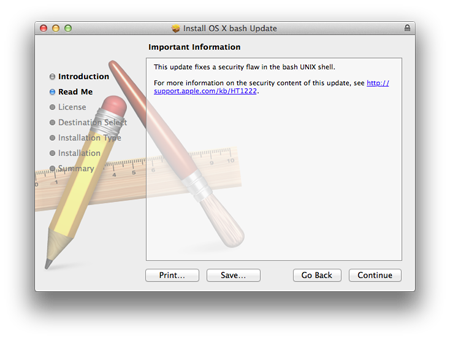
Apple already released an update that’s recommended for all users and all versions of OS X. Even if you never use Terminal it’s strongly recommended that you install the update, since you don’t need to use the app to be vulnerable.
The update itself is only around 3.5MB and there’s a different download for each of the major versions of OS X. Sadly, if you’re running the Yosemite Beta you’re out of luck for now.
Patches:
- Mavericks (OS X10.9.5+)
- Mountain Lion (OS X 10.8.5)
- Lion (OS X 10.7.5)
The update isn’t available as a system update yet, so use the links above to get yourself protected now. While desktop machines are not the major at-risk computers in this vulnerability, it’s a good idea to keep your Mac as safe as possible, so get patched and get ready for the next Internet-shattering flaw that’s surely right around the corner.




4 thoughts on “What is Shellshock and How to Protect Against It”
I ran the command as directed and got the Fix Me! response. After downloading and installing the patch for 10.9.5 I reran the command and it still responds with Fix Me!
I did the same, shut my Mac down, restarted and still get the Fix Me! response.
Same goes here. After applying the Shellshock patch on MacOS X 10.9.5, the result from the command is still:
Fix Me!
Machine:~ user$ Read more at https://www.applegazette.com/news/shellshock-protect/#S5SjtrJafCi8SgA5.99
Looks like there was an issue with the quotes. Here is the updated code:
env x=”() ; echo vulnerable” bash -c “echo Fix Me!”