The world of digital security can be a scary one. With hackers in the news and a big ransomware scare just recently wrapping up, folks have good reason to be concerned. Staying secure online is crucial, and it starts with good security habits. But what if you’re concerned that someone is spying on you through your Mac’s webcam? Can you find out if a rogue app is accessing your Mac’s webcam?
It isn’t just an idle question. Not too long ago, there was a fad among troublemakers and hackers to make online “slaves.” It sounds worse than it actually is: basically, dumb kids (and some childish adults, I’m sure) would take over the webcams of unsuspecting targets and watch them go about their day. Sometimes, they would catch glimpses of people undressing, but the point was to invade someone’s privacy. This was based on a Windows exploit, but a ounce of prevention is worth a pound of cure.
Using lsof to Find Out What App is Using Your Webcam
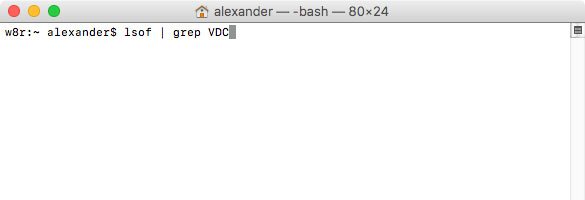
The “stock” way to find out which app is using your webcam on a Mac is, unfortunately, not excellent. It requires some Terminal commands and a little bit of computer know-how. There are simpler ways that use off-the-shelf software, which we’ll cover below. If you’re comfortable with Terminal, however, you can use the Terminal command lsof to get a list of applications currently attempting to access your webcam.
1. Open Terminal (Applications/Utilities/Terminal.app).
2. If you have a built-in webcam (like with a MacBook Pro or iMac), copy and paste the command below and press “Enter.” You can also type in the command, but be sure to be 100% accurate.
lsof | grep AppleCamera
If you have a third-party webcam (like a Logitech model) copy and paste the following command and press “Enter.”
lsof | grep VDC
lsof command tells you what process or application is using a specified system resource. By running lsof “naked,” or without flags, we would normally get a list of all the processes doing just about anything on our Mac. Then, we search through that list using grep to find references to the appropriate webcam interface.
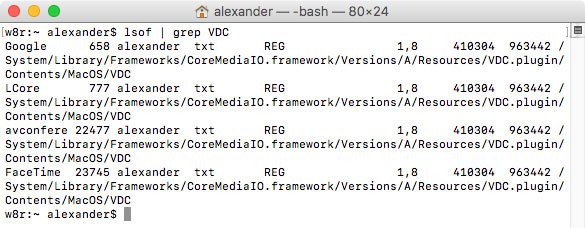
3. In this case, the command will return a list of all the applications currently using (or thinking about using) your webcam.
Annoyingly, this list will likely include some extraneous applications. You’ll see stuff like the third-party software that runs your camera (if any). You’ll also often see Google Chrome listed. Even with this imperfect list, however, you’ll have a place to start scanning for suspicious or unexpected applications to investigate.
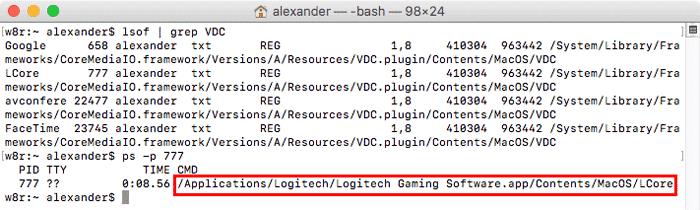
This list, though cryptic looking, is decipherable. If you look at the beginning of each line, you’ll see some familiar program names: in this case, Google and FaceTime. There’s also some unusual ones, like LCore and something called “avconfere.” Let’s investigate the odd ones.
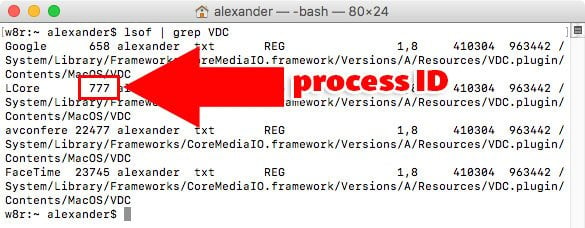
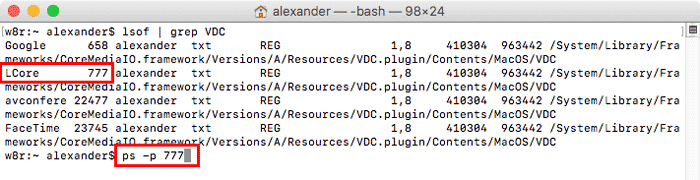
4. To find out more about this processes, I can us the ps -p command, along with the process ID. The process ID is the number next to each program’s name, and it’s just a number that allows you to specify which particular program you want to investigate with Terminal.
5. For example, the following command will tell me more about the LCore process:
ps -p 777
If you’re curious about what we’re doing, the -p flag allows us to use ps to investigate the origin and status of a running process as specified by its process ID.
6. As we can see, that’s the Logitech kext that’s running my Logitech webcam, so that’s no danger. I can tell thanks to the location of the file, as well as a little Googling to confirm my suspicions.
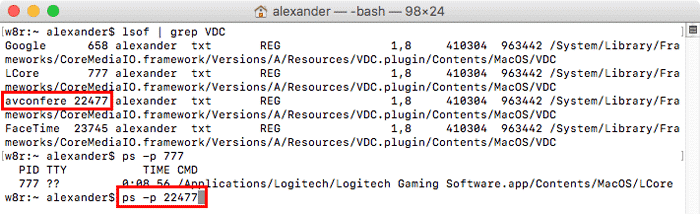
7. Let’s try the same trick on the “avconfere” process using the command below:
ps -p 22477
8. That actually “avconferenced” which is the daemon that handles all webcam requests on macOS, so that’s also safe too. I know this because I Googled it, which you should do for any unusual processes. I also suspect it’s safe because it’s in the “libexec” folder, which contains system daemons and utilities. Of course, a clever attacker might disguise their process in that way, so always investigating anything you don’t recognize or understand.
Quitting Apps Using Your Webcam
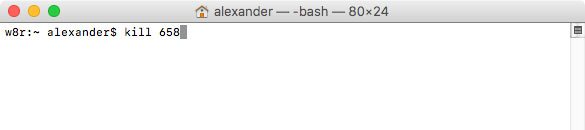
If you do find a malicious application, you can quit it from the command line using the kill command.
1. Use the above process to determine the process ID of the application using your webcam.
2. Type kill #### where #### is the process ID of the application you want to quit. For example, to kill Chrome, I would type the following:
kill 658
Using Oversight To Get Notified When Your Webcam Is Enabled
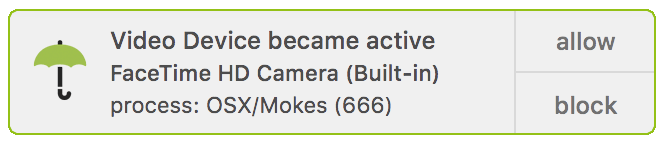
lsof has limitations, listing all the apps that might attempt to access your webcam (like Chrome) even if they’re not doing so currently. The freeware app, Oversight, which was developed by an ex-NSA hacker, is a good alternative. Oversight will alert you whenever your camera or microphone becomes active, and let you know which application has started using it. You can then approve or deny the usage directly from a notification.
1. Download and install Oversight.
2. When an application wants to use your webcam, Oversight will generate a notification.
3. Click Allow to allow the app to use your webcam, or Block to deny the usage.
Conclusion
There’s a couple of ways to find out which application is using your Mac’s webcam. And remember that built-in Mac webcams will always show their green “in use” light when operational. This is thanks to the physical wiring of the device. For power to reach the camera, it must also illuminate the LED. Thanks to this design, it’s hard to imagine a software exploit that would disable the light, but caution is rarely regrettable. If you’re really freaked out, don’t forget the lowest tech solution of all: a piece of tape stuck over your webcam’s lens.
You might also like the following:




2 thoughts on “Find Out What App Is Using Your Webcam on Your Mac”
I’ve found that for OSX 10.4+ (Mojave onwards) you can use:
~ user$ lsof | grep “FaceTime”
Thanks a lot for the article. I have been searching for a command to use in my python project, for checking if MAC webcam is used(if camera is on or off) by any application or not.
(Even I do not need the exact process id or name which use the camera)
Till now I have found already tried your both recommendations, but unfortunately both of them did not work properly:
1-lsof | grep “AppleCamera”, lsof | grep “iSight” or lsof | grep “VDC” commands:
These commands show the process ids and names which use the camera.
But the problem is that these commands show also many processes which are not exactly using the camera too. For example,
in same cases even if Facetime is minimized to dock(it means that the camera is not on, in idle mode.)
these commands show Facetime application as an application which is occupying the camera (although it is not).
Or in same cases some applications are shown as processes which use the camera, although the camera connection of application was already closed before.
2-oversight tool:
Unfortunately it does not support any command line commands, so it is not possible to use in my python project.
Do you have an other idea to detect MAC camera status?
Thanks a lot in advance.