The SSH configuration file on your Mac controls how secure shell, aka SSH, operates. It can be used for simple alternations, like changing the ssh port on your devices, can often eliminate a huge number of ssh “cold calls” on your machine, the ssh configuration file can do much more than that.
Where is the SSH configuration file?
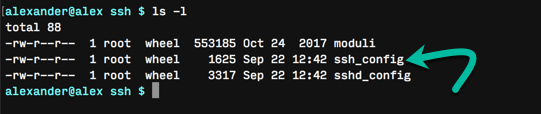
On macOS systems, the configuration file is found at “/private/etc/ssh/ssh_config,” which is symlinked to “/etc/ssh/ssh_config” for compatibility.
A second, user-specific ssh_config is found at “~/.ssh/ssh_config.” If it exists, this file supersedes the system-wide configuration file. This file sets user-specific options without changing the system’s configuration.
Going forward, we will refer to this configuration file as “ssh_config” for clarity and simplicity. You can edit whichever one is better suited to your purposes.
What is the ssh_config file and what does ssh_config do?
The ssh_config file is used to control how secure shell, better known as the ssh terminal command, operates on your system. The ssh configuration file is organized by hosts. Each host contains specific settings for that host. Wildcards like * can be used to match multiple hostnames with a single declaration.
Options are declared using a key/definition pair. A detailed explanation of each key’s functionality can be found on the ssh_config man page. We will cover the most relevant collection of changes below.
Editing the ssh_config file
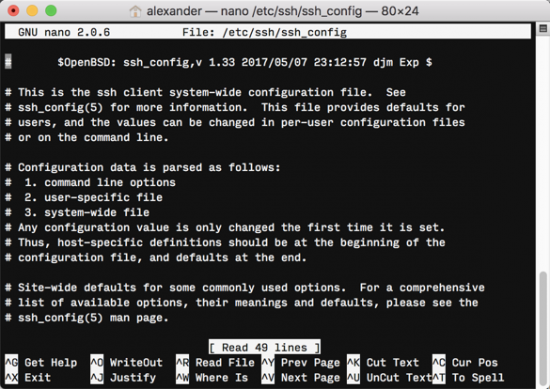
To edit the ssh_config file, open a Terminal window and edit the file with your preferred text editor. We will use nano in this demo, but vi or emacs can be used instead.
sudo nano /etc/ssh/ssh_config
Hardening your SSH configuration
Confirm SSH Protocol 2
By default, SSH should use Protocol 2, the more secure protocol. The older protocol, aptly named Protocol 1, works with a weaker integrity check and is generally less secure.
However, older systems may request Protocol 1. To explicitly set the stronger protocol, use the following in your ssh_config:
Protocol 2
You can also implicitly set your protocol by using Ciphers. This will automatically set Protocol to 2.
Ciphers aes128-ctr,aes192-ctr,aes256-ctr
Disallow empty password
This key bans logging in to the ssh system without using a password, effectively requiring all users to set passwords. Change AllowEmptyPassword to No.
Disallow root login
Prohibiting root login will dramatically reduce the damage that an attacker can do to your system. However, it might make your job a little harder, depending on what you need to do. Options for PermitRootLogin include “yes,” “without-password,” “forced-commands-only,” or “no.” The default is “yes.”
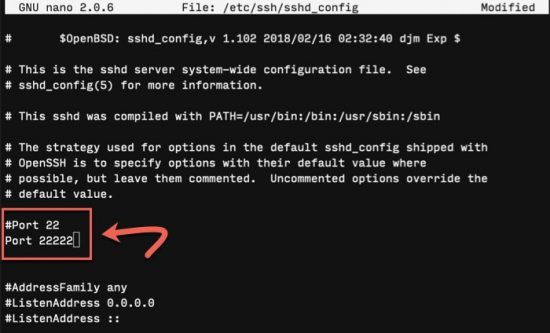
Change the ssh port number
Changing the port used by ssh can help you avoid simple attacks on your server. While this won’t work against an attacker scanning for open ports, it can reduce the number of automated dial-ins you get. Before setting a new port, ensure it’s not used by any other program or service.
The default SSH port is port 22. To adjust the port, edit the main ssh daemon at “/etc/ssh/sshd_config.” You’ll want to add a new line specifying the port following the syntax Port XXXXX.
Restrict access to specific users
If you have multiple people who access your server, you may want to restrict the use of ssh altogether. These tools allow you to restrict SSH use to specific users: DenyUsers, AllowUsers, DenyGroups, and AllowGroups. Each line supersedes the last, so think about order carefully.
AllowUsers ramesh john jason AllowGroups sysadmin dba DenyUsers cvs apache jane DenyGroups developers qa
Customizing SSH Configurations
Creating aliases
You can simplify commonly-used SSH commands with aliases. Like bash aliases, these allow you to replace a long command with a short string.
For example, the following alias allows the user to connect to the dev server with the specified options simply by typing ssh dev at the command line.
Host dev
HostName dev.example.com
Port 22222
User foobar
This runs the following command when executed:
ssh foobar@dev.example.com -p 22222
Authentication with secure keypairs
SSH is more secure and convenient when used with public/private keypairs for authentication, rather than passwords. The ssh_config file can declare a specific key for a specific host using the IdentityFile key.
Host dev
HostName dev.example.com
Port 22222
User foobar
IdentityFile ~/.ssh/dev.example.key
As in the previous examples, this SSH command with be run with ssh dev, executing the following command-line equivalent command:
ssh -i ~/.ssh/dev.example.key foobar@dev.example.com -p 22222
Conclusion
Most of the ssh_config options exist to provide more convenient ways to perform specific tasks using the ssh command. It’s a way to configure complex aliases and shortcuts that helps increase security by making the more secure parts of ssh easier to use.
If you’re interested in improving your Terminal skills, you might be interested in the following posts:



2 thoughts on “Pro Terminal Commands: Editing the SSH Configuration File”
Thanks for the article. On my Mac, the user-specific config file was “~/.ssh/config” , not “~/.ssh/ssh_config”
when you edit the file do the changes take effect immediately or only when sshd restarts? OR ?