 A new Trojan for OS X that operates remotely to steal user information and crash a Mac has been found by security researchers Sophos.
A new Trojan for OS X that operates remotely to steal user information and crash a Mac has been found by security researchers Sophos.
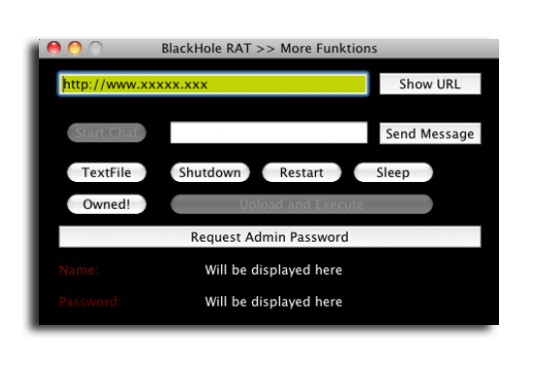
The “backdoor Trojan” called BlackHole Rat and dubbed MusMinim-A by security researchers operates in the background of an infected Mac. MusMinim’s biggest threat to users is the ability to display fake prompts asking the user for their administrator name and password. This gives the Trojan complete access to your Mac and has the potential to execute malicious commands, collect passwords and user IDs or crash your Mac.
Currently the Trojan can execute shell commands, prompt users to click a URL via a popup and wreaks havoc on an infected Mac by forcing the machine to shut down, restart or enter sleep mode. Side effects of the Trojan include text files littering a user’s desktop and alerts consuming the screen which leaves no option but to restart.
The Malware’s user interface reveals it is under ongoing development and informs the user of its malicious intentions:
“I am a Trojan Horse, so i have infected your Mac Computer. I know, most people think Macs can’t be infected, but look, you ARE Infected!
I have full controll over your Computer and i can do everything I want, and you can do nothing to prevent it.
So, Im a very new Virus, under Development, so there will be much more functions when im finished.”
The Trojan’s interface controlled by a hacker
An analysis by SophosLabs revealed it’s a variant of the popular Windows Remote Access Trojan darkComet. MusMinim’s development and infection isn’t without irony. MusMinim’s author calls his Trojan “Black Hole RAT” but ‘Black Hole’ is the name of an App that increases a user’s security by removing sensitive information that could be exploited.
Sophos published data is has collected on the Trojan to help users identify OSX/MusMinim.
Apple is starting to take greater strides when it comes to security and is giving prominent security researchers a sneak peak at OS X Lion.
Hackers, Malware writers and programmers with malicious intents are taking notice of OS X’s growth. As Apple products increase in market share, they become more enticing to write viruses, Trojans and Malware for as the amount of targeted users increases. However, there are some ways you can protect yourself.
How To Protect Yourself
While the number of viruses, Trojans and other Malware available for the Mac is far fewer in number compared to Windows, security Software exists. Sophos, — which has years of experience finding flaws in Operating Systems and helping users guard themselves against vulnerability — maintains and distributes a free Anti-Virus scanner for Mac users.
Using common sense when downloading files, exchanging information and handling sensitive data are ways to protect yourself online. Buying Software from trusted sources removes the risk of going to shady yet convenient file hosting sites. Being wary of sites that distribute Apps and being able to identify what’s bogus or what could hurt your computer makes it harder for hackers to take advantage of unsuspecting users.
Sophos echoes the same words of caution:
“Trojans like this are frequently distributed through pirated software downloads, torrent sites, or anywhere you may download an application expecting to need to install it,





6 thoughts on “New OS X Trojan Found In The Wild & How To Protect Yourself Against It”
Looks like yet another “Trojan” for the Mac that users need to seek out, download, and install themselves in order to work.
However, that little factoid isn’t mentioned by Sophos, as they finally really want to sell some Mac AV software – which is about as useful as a sharp stick in the eye.
Given the general lack of credibility for security firms for phony virus claims in order to sell their vapor ware, I elect to ignore crap like this. The only fact is that internet journalist and bloogers have even less credibility than companies like Sophos. The question is, who are the real BlackHole rats?
I’ve always found it hilarious that these hacking morons can’t spell the simplest of words.
We need independent evidence of this claim.
I am not accusing Sophos of anything but let’s face it, there is enormous commercial advantage for the company to make claims which as exaggerated or …. worse ….
Sophos is wrong: the old security through obscurity argument was debunked years ago. Mac OS X has been a huge target for hackers for ten years but is quite secure.
True to say it does sound like a conflict of interest hearing of such malware reports coming from an anti-malware developer, but who else would be looking for such weaknesses and exploits by trojans and viruses than those who do this kind of work? That being said, OSx still has my vote of confidence in its security, and hopefully manages to control the spread of viruses and trojans as it continues to grow in popularity.